In the August 2023 Security update (SU) for Exchange Server 2016 and Exchange Server 2019, there was a work around that had to be put in place to remove the Token Cache Module in IIS to mitigate a vulnerability. Microsoft provided the script and you could apply it to all servers in your environment or selected ones.
When the October 2023 Security Update (SU) was released, Microsoft advised you could rollback this work around but only if you applied the latest Windows Updates for your operating system.
You can head over to the link below that details all this below:
In my lab, I applied the latest windows updates, tested on both Windows Server Core and Windows Server with a GUI. I then applied the October Security Update for Exchange Server 2019 and after a reboot, rolled back the work around.
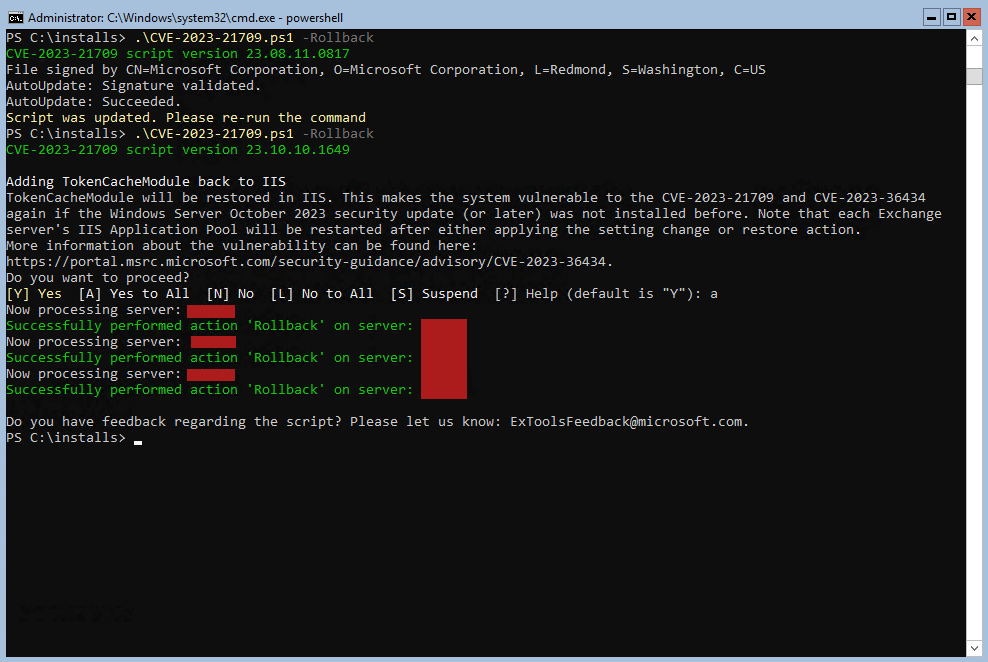
What is nice about the script is that it checks for updates and if there are any, updates and then tells you to re-run it. Below is the output of this and Token Cache has been enabled again in IIS.
While I did not notice any performance hits in the environments where it is applied, some have reported it so just take note, if you are behind with applying Exchange Server updates, maybe run the October 2023 Windows updates and then the October 2023 Security Update for Exchange Server that includes the fix then you won’t need to do the work around.
Hope it helps.
